IMPORTANT REALITY: That "secure" business VPN your Calgary engineering firm or Vancouver accounting office is using to access company files? It might be creating significant security vulnerabilities that cybercriminals can exploit. While consumer VPNs like Proton market themselves as privacy solutions, using them for secure remote access Calgary and Vancouver businesses need is like installing a deadbolt on your front door while leaving your windows wide open.
Important Security Information for Calgary & Vancouver Businesses
The real cost extends beyond productivity loss to serious business impact. A misconfigured port forward through a consumer VPN can give attackers access to your network, client data, and intellectual property.
The Limited Security of Consumer VPNs for Calgary & Vancouver Businesses
Before we expose the dangerous gaps, let's acknowledge what consumer VPNs like Proton actually do well—and why this creates a false sense of security for businesses:
Privacy & Anonymity
Helps individuals hide their IP address and encrypt their browsing activity from ISPs and trackers.
Geo-Restriction Bypass
Useful for personal streaming, accessing region-locked content, or maintaining privacy while traveling.
Strong Encryption
Uses industry-standard protocols to protect traffic from eavesdropping on public WiFi.
No-Logs Policy
Ensures user activity isn't recorded or stored, maintaining personal privacy.
Open-Source Transparency
Code can be audited for security vulnerabilities, building trust through transparency.
Free Tier Available
Offers basic functionality without cost, making privacy accessible to everyone.
Key Challenge: These consumer-focused features can create a false sense of security. Business owners see "military-grade encryption" and "secure tunnel" and may assume their company data is fully protected. However, this isn't the case. Consumer VPNs only encrypt the pathway to the internet—they don't secure your internal business resources.
Key Limitation: Why Business VPN Calgary Solutions Require More Than Consumer Tools
Important Distinction: Proton VPN's architecture is designed primarily for routing traffic through their servers to the public internet. When your Calgary engineering team needs to access internal project servers, or your Vancouver accounting firm needs the company database, Proton VPN doesn't provide that capability. This is where proper cybersecurity services and business network security solutions become essential.
What Proton VPN Can't Do:
- ❌ Connect into your company's private network (on-premises or cloud)
- ❌ Enable staff to securely access internal file shares
- ❌ Facilitate remote management of internal systems
- ❌ Provide granular access controls based on user roles
- ❌ Integrate with Microsoft Active Directory or Entra ID
- ❌ Enforce device compliance before granting access
- ❌ Provide application-specific access controls
- ❌ Support site-to-site connectivity for branch offices
In other words, it's only half of what businesses actually need. Employees don't just need privacy while browsing; they need secure tunnels into the company's network itself.
Why 'Encrypted' Doesn't Mean 'Secure'
Common Misconception: Business owners hear "encrypted tunnel" and may assume comprehensive protection. However, Proton VPN only encrypts traffic to their servers, not to your business resources. Your employees remain vulnerable when accessing company files, databases, or applications.
Important Consideration: When your Calgary or Vancouver employees try to reach:
Proton VPN doesn't protect these resources. Your "secure" tunnel ends at their server, leaving your valuable business assets exposed to potential threats.
The Armored Car to Train Station Analogy: Why Consumer VPNs Miss the Mark
IMAGINE THIS SCENARIO: You need to safely deposit your company's most valuable assets at the bank. You hire an armored car service (Proton VPN) to transport you securely from your house (your computer) to the public train station (Proton's servers). The armored car does its job perfectly—bulletproof windows, armed guards, complete protection during that specific journey.
🚗➡️🚉➡️🏦 The Journey Breakdown
Your Computer/Office
Starting point - where your employee begins their work session
Public Train Station (Proton Servers)
Safe arrival at the VPN endpoint - encrypted journey complete
Your Business Network/Files
Final destination - where your valuable company data lives
BUT HERE'S THE PROBLEM: Once you arrive at the train station (Proton's servers), the armored car service says "This is as far as we go. You're on your own now." To reach the bank (your business network), you must:
🚂 Board a Public Train
Risk: Travel unprotected through public infrastructure where anyone can see you, follow you, or attack you. This is your data traveling from Proton's servers to your business network.
🗺️ Navigate Alone
Risk: No guidance or protection for the most dangerous part of the journey. Your employee must figure out how to safely access internal resources without any VPN protection.
🎯 Become a Target
Risk: Criminals at the train station (cybercriminals monitoring Proton exit points) can follow you to discover where your business "bank" is located.
The Key Insight
Your business is paying for security in the wrong place. The armored car (Proton VPN) protects you during a relatively safe leg—from your computer to their servers. But the more vulnerable part—accessing your actual business resources—happens without VPN protection.
✅ What Proton VPN Protects:
- Your internet browsing from prying eyes
- Your location when accessing public websites
- Your connection to their servers
❌ What Proton VPN DOESN'T Protect:
- Access to your company file servers
- Connection to your business applications
- Your most valuable business data and systems
It's like hiring bodyguards for your walk to the airport, then flying commercial with no security while carrying valuable assets.
Where Proton VPN CAN Add Business Value (When Used Correctly)
FAIR ASSESSMENT: Before diving into the dangers of using Proton VPN incorrectly, let's acknowledge where it can actually provide legitimate business value. Consumer VPNs aren't inherently evil—they're just designed for a different purpose. Here are scenarios where Calgary and Vancouver businesses can safely leverage Proton VPN as additional security:
✅ LEGITIMATE BUSINESS USE CASES
These scenarios work because you're adding a layer of protection to services that already handle their own encryption and security:
🌐 HTTPS Web Applications
How it helps: Accessing cloud-based business tools (Salesforce, Office 365 web apps, project management systems) through Proton VPN can hide your business IP from potential attackers monitoring these services.
Why it works: The applications already use SSL/TLS encryption. Proton VPN adds IP masking without breaking functionality.
🖥️ Remote Desktop Services
How it helps: Connecting to Windows Remote Desktop (RDP) or other remote access services through Proton VPN can obscure your source IP, making it harder for attackers to identify and target your business.
Why it works: RDP already has its own authentication and encryption. The VPN adds anonymity without interfering with the connection.
🔒 IP Whitelisting Scenarios
How it helps: Some cloud services or vendors require IP whitelisting. Using Proton VPN's static IP addresses can simplify management when you have remote employees in different locations.
Why it works: You're not trying to access internal resources—you're presenting a consistent public IP to external services.
🛡️ Public WiFi Protection
How it helps: When Calgary or Vancouver employees work from coffee shops, hotels, or airports, Proton VPN protects against man-in-the-middle attacks on unsecured networks.
Why it works: You're protecting the connection to the internet, not trying to create business network access.
🔍 Threat Research & Monitoring
How it helps: IT security teams can use VPNs to research threats, investigate suspicious websites, or monitor competitors without exposing the company's real IP address.
Why it works: This is legitimate operational security for activities that don't require internal network access.
🌍 Geographic Access Requirements
How it helps: Accessing region-locked business services, compliance with location-based regulations, or testing geo-targeted marketing campaigns.
Why it works: You're using the VPN for its intended purpose—changing your apparent location for legitimate business needs.
⚠️ CRITICAL DISTINCTION: Layer of Protection vs. Primary Solution
The key difference: In all these scenarios, Proton VPN is adding an additional layer of protection to services that already handle their own security. It's not being asked to create secure access to unprotected internal resources.
✅ ACCEPTABLE: Additional Layer
- HTTPS website ➕ VPN = Extra anonymity
- Encrypted RDP ➕ VPN = Hidden source IP
- Cloud app ➕ VPN = Geographic flexibility
Result: Enhanced security without breaking anything
❌ DANGEROUS: Primary Solution
- Internal file server ➕ VPN = Still completely exposed
- Unencrypted database ➕ VPN = No real protection
- Internal applications ➕ VPN = Massive security holes
Result: False sense of security leads to catastrophic breaches
🧠 THE SMART APPROACH
Use Proton VPN as a supplemental tool, not your primary business security solution. Think of it like wearing a raincoat—great protection when you're already dressed appropriately, but useless if you're trying to use it as your only clothing.
For Calgary accounting firms, Vancouver engineering companies, and law offices: Use Proton VPN for legitimate privacy needs, but invest in proper enterprise solutions for accessing your critical business systems.
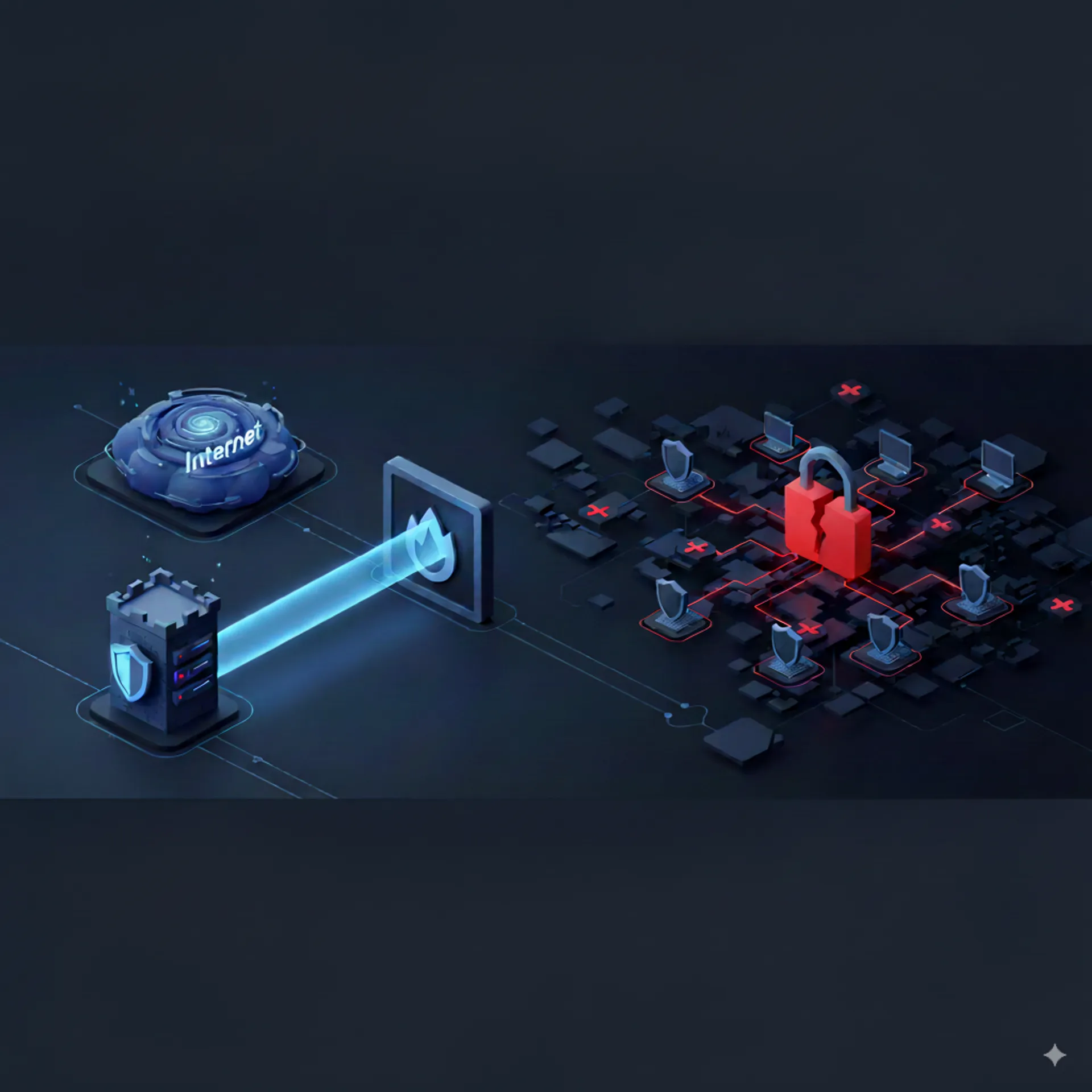
PORT FORWARDING RISKS: Why Calgary & Vancouver Businesses Face SMB File Sharing Security Threats
This is where serious risks emerge: When Calgary and Vancouver businesses realize Proton VPN can't access their internal resources, they often make a critical error. They start opening ports and creating forwarding rules that essentially create vulnerabilities in their firewall. It's like installing a bank vault door, then leaving a key under the doormat.
The Port Forwarding Trap:
To make internal resources accessible through Proton VPN, IT teams typically:
- Configure Proton VPN to provide a static gateway IP
- Whitelist that IP on corporate firewalls
- Set up port forwarding/NAT rules to internal services
- Create DNS records pointing to the gateway
- Monitor and maintain the configuration
🚨 Increased Attack Surface
Every forwarded port increases your attack surface. Automated attack tools continuously scan for exposed ports. Your business becomes more visible to potential attackers.
🎯 Network Visibility Risks
Your DNS records become public information. Threat actors maintain databases of exposed business networks. Your company's IP address and open ports become discoverable.
🔓 Credential Attack Risks
Exposed services face constant brute force attacks. Automated tools can attempt millions of password combinations per day against open ports. Even strong passwords become vulnerable to sustained attacks.
⚖️ Compliance Concerns
Exposed services may violate compliance standards. PIPEDA, SOC 2, and PCI-DSS regulations require proper security controls for business services. Non-compliance can result in significant penalties.
🔧 IT Management Challenges
Port forwarding creates ongoing management overhead. Each exposed service requires monitoring, updating, and security maintenance. This increases complexity and potential points of failure.
📊 Limited Visibility
Port forwarding provides minimal security logging. Without detailed audit trails, it's difficult to detect unauthorized access attempts or investigate security incidents effectively.
CASE STUDY: How SMB Shares Become Ransomware Highways
THE RANSOMWARE REALITY: SMB file shares exposed through port forwarding are among the most targeted attack vectors by cybercriminals. Here's exactly how consumer VPN solutions turn your file shares into ransomware superhighways:
📊 The SMB Security Risk Pattern
To make your "secure" file shares accessible through Proton VPN, your IT team will be forced to:
- Expose ports 445 and 139 (commonly targeted ports) to internet access
- Whitelist third-party gateway IPs that may change without notice
- Create DNS records that reveal network entry points
- Rely on obscurity rather than proper security controls
This approach significantly increases security risks rather than reducing them.
TCP Port
HIGHLY TARGETED & EXPLOITED
Average breach cost
IN CANADA (2024) - IBM
⚠️ Why This Significantly Increases Risk:
- High Attack Interest: Automated attack tools continuously scan port 445. Exposing it significantly increases your visibility to potential attackers.
- Ransomware Target: WannaCry, NotPetya, Ryuk, and many other ransomware variants specifically target exposed SMB shares for network propagation.
- Network Segmentation Bypass: Port forwarding can undermine network segmentation, reducing the effectiveness of firewall protections.
- Compliance Issues: Major frameworks (PCI-DSS, PIPEDA, SOC 2) require proper security controls. This configuration may fail compliance requirements.
- Lack of Identity Controls: Basic port forwarding cannot distinguish between legitimate users and unauthorized access attempts. All connections are treated equally.
- Lateral Movement Risk: Successful SMB exploitation can provide attackers with a foothold for lateral movement throughout the network, potentially compromising additional systems.
What Calgary & Vancouver Businesses ACTUALLY Need: Enterprise VPN Solutions
Professional Approach: To properly protect your Calgary or Vancouver business, consider enterprise-grade solutions that were specifically designed for business security requirements. Professional managed IT services can help implement these solutions properly:
✅ True Network Access
Site-to-site tunnels that securely connect remote workers directly into the corporate network, not just to the internet.
✅ Identity Integration
Seamless integration with Microsoft Entra ID, Active Directory, or other identity providers for single sign-on.
✅ Granular Controls
Role-based access ensuring users only reach the resources they need, nothing more.
✅ Device Compliance
Verification that connecting devices meet security standards before granting access.
✅ Central Management
Single dashboard for monitoring, auditing, and controlling all remote access.
✅ Scalable Performance
Infrastructure built to handle your entire team without degradation.
The HIDDEN Costs of Cheap VPN Solutions
The Full Cost Picture: While consumer VPNs appear cost-effective at $20/month, they can create hidden expenses and security risks that impact your business. Here are the real costs that consumer VPN vendors typically don't discuss:
💸 Hidden Costs of Consumer VPN Solutions:
🕳️ Shadow IT Risks
$127,000 average cost: When employees can't access what they need, they create dangerous workarounds—personal cloud accounts, USB drives, remote desktop exposures. Each one is a potential breach point.
📋 Compliance Challenges
Significant penalties possible: PIPEDA violations can result in substantial fines. Failed compliance audits may impact client relationships and business operations. Regulatory requirements are increasingly strict.
🔍 Investigation Impossible
Insurance complications: In the event of a breach, insurers typically require detailed access logs. Consumer VPNs often provide limited logging, which could complicate insurance claims.
📞 Support Desert
Limited business support: Consumer VPN support teams typically cannot assist with business network issues. Extended downtime during critical hours can impact productivity and revenue.
🐌 Performance Nightmare
Performance inconsistency: Shared consumer infrastructure can result in variable connection speeds and reliability, impacting team productivity and user experience.
⚖️ Legal Liability
Terms of service restrictions: Many consumer VPN services prohibit business use in their terms. Using services outside their intended scope could complicate legal and insurance matters.
Enterprise VPN Vancouver & Calgary: Solutions That Actually Protect Your Business
Purpose-Built Solutions: Rather than adapting consumer tools for enterprise needs, consider purpose-built solutions designed to protect Calgary and Vancouver businesses while enabling secure remote work. Many of these solutions are available through cloud services and IT consulting partnerships:
Enterprise VPN Appliances
Examples: Fortinet, Cisco Meraki, Sophos, OPNsense
- Hardware or virtual appliances
- Integrated threat protection
- Centralized management
- Site-to-site connectivity
Best for: Companies with on-premises infrastructure
Zero Trust Network Access
Examples: Cloudflare Access, Tailscale, Netbird, Twingate
- Application-specific access
- No exposed attack surface
- Cloud-native architecture
- Device posture checking
Best for: Professional services firms with cloud-based workflows
Managed Business VPN Services
Examples: MSP-provided solutions
- Pre-configured for your needs
- 24/7 monitoring and support
- Regular security updates
- Compliance assistance
Best for: Calgary and Vancouver SMBs without dedicated IT staff
Cloud-Native Solutions
Examples: Azure VPN, AWS Client VPN
- Integrated with cloud services
- Pay-as-you-go pricing
- Global availability
- Native security features
Best for: Cloud-heavy workloads
SD-WAN Solutions
Examples: VMware SD-WAN, Cisco Viptela
- Optimized for multiple locations
- Integrated security stack
- Application-aware routing
- Centralized orchestration
Best for: Multi-site businesses
Microsoft Solutions
Examples: Always On VPN, Entra Private Access
- Native Windows integration
- Conditional access policies
- Seamless authentication
- Included with some licenses
Best for: Microsoft 365 organizations
Secure Remote Access Calgary & Vancouver: Don't Become the Next Cyber Attack Statistic
Taking Action: Delaying proper business security implementations increases risk exposure over time. Threat actors actively scan for and target businesses using inadequate security solutions, making timely upgrades important for maintaining security posture.
Key Decision Factors for Calgary & Vancouver Businesses:
Team Size & Growth
How many users need access now and in 12 months?
Resource Types
What applications, files, and systems need remote access?
Compliance Requirements
What regulations govern your data handling?
IT Resources
Do you have dedicated IT staff or need managed services?
Budget Reality
What's the true cost including setup, management, and risk?
Integration Needs
What existing systems must the solution work with?
⚠️ The Bottom Line
Using Proton VPN for business network access significantly increases security risks rather than providing proper protection.
Just as you wouldn't use a bicycle lock to secure a bank vault, consumer privacy tools aren't designed for business network security. The cost of inadequate security can include significant financial and operational impacts.
Delaying proper business security implementation increases exposure to sophisticated cyber threats. The modest savings from consumer VPNs may not offset potential costs from security incidents, regulatory fines, and business disruption.
Consider implementing appropriate business security measures to protect your organization's assets and operations.
🛡️ Professional Security Assessment
Assess your current security posture. Implementing appropriate security measures helps reduce exposure to cyber threats. Calgary AEC firms and Vancouver accounting and law offices benefit from professional security assessments.
Huntertech's certified security team, serving Calgary and Vancouver AEC, accounting, and law offices since 2008, can immediately:
- Assessment: Conduct a comprehensive vulnerability assessment of your current VPN setup
- Implementation: Design and deploy enterprise-grade business VPN Calgary and Vancouver solutions
- Security: Implement Zero Trust access controls for network protection
- Compliance: Ensure adherence to Canadian regulations and industry standards
- Support: Provide ongoing monitoring and incident response
- Experience: Deliver solutions trusted by Calgary and Vancouver businesses
Proactive security measures are more effective than reactive responses to incidents.
Schedule a security consultation to discuss your needs.
Frequently Asked Questions
Can't I just use Proton VPN's business plan for my company?
While Proton VPN offers a business plan, it still fundamentally provides internet tunneling rather than true network access. Your employees would still need additional solutions to access internal file servers, applications, or databases. For Calgary engineering firms and Vancouver AEC, accounting, and law offices needing genuine secure remote access to company resources, purpose-built business VPN Calgary solutions or Zero Trust Network Access are essential for proper SMB file sharing security.
What are the specific risks of exposing SMB file shares through port forwarding?
SMB ports (445/139) are among the most targeted by cybercriminals, representing serious port forwarding risks for business networks. Exposing them through port forwarding, even behind a VPN gateway, creates vulnerabilities to ransomware attacks like WannaCry and NotPetya. Most compliance frameworks explicitly prohibit exposing SMB directly to the internet. Calgary AEC firms and Vancouver accounting and law offices handling sensitive client data face significant liability if breached through exposed SMB file sharing security vulnerabilities.
How much more expensive are business VPN solutions compared to Proton VPN?
While Proton VPN business plans start around $8-12 per user/month, proper enterprise VPN Vancouver and Calgary solutions typically range from $15-40 per user/month. However, the total cost of ownership often favors business solutions when you factor in reduced security risks, eliminated workarounds, proper support, and integrated features. Many Calgary and Vancouver managed IT services providers specializing in AEC, accounting, and law offices offer bundled solutions that provide better value than piecing together consumer tools.
What's the difference between Zero Trust Network Access and traditional VPN?
Traditional VPNs provide broad network access once authenticated, while Zero Trust Network Access (ZTNA) grants access only to specific applications on a per-session basis. ZTNA verifies user identity, device health, and context for every access request. For Vancouver law offices and Calgary AEC firms with hybrid work models requiring secure remote access, ZTNA offers superior VPN security that professional services firms need by eliminating the concept of a trusted internal network.
Can we use Proton VPN alongside our existing business VPN?
While technically possible, running multiple VPNs simultaneously often causes conflicts, performance issues, and routing problems. Employees might inadvertently bypass security controls by using the wrong VPN. It's better to invest in a comprehensive business VPN Calgary or Vancouver solution that handles both internet privacy and internal access needs. Calgary and Vancouver IT consultants specializing in AEC, accounting, and law office cybersecurity can help design a unified approach that meets all requirements.